![]()
Security Operations Center (SOC) is a critical part of an organization’s IT security department for addressing threats, vulnerability, and for assessing and managing cyber attacks. However, Security Operations Center that works well for an organization requires best security professionals, processes, and technology.
A SOC is an effective incident response system of an organization that manages all incidents in an enterprise, including identifying possible cyber attacks, giving situational alertness through detection, and providing fast response capabilities. Yet, most SOCs continue to fall short in keeping some type of cyber attacks, such as the recent Wanna Cry Ransomware attack, out of the enterprise. Follow these best practices for running security operations center of your organization.
Collaboration among SOC people:
A well-designed SOC empowers administrators, analysts, and security professionals to see attacks on the network and helps them leverage incident management tools. Their responsibilities should be defined and communicated.
SOC tools must support unique roles of each person and make it enable to deliver near real-time reports based on unique roles. Everyone should know how and when to escalate events to higher level administrative officer to enforce the remediation action immediately.
Implement intelligence-driven SOC:
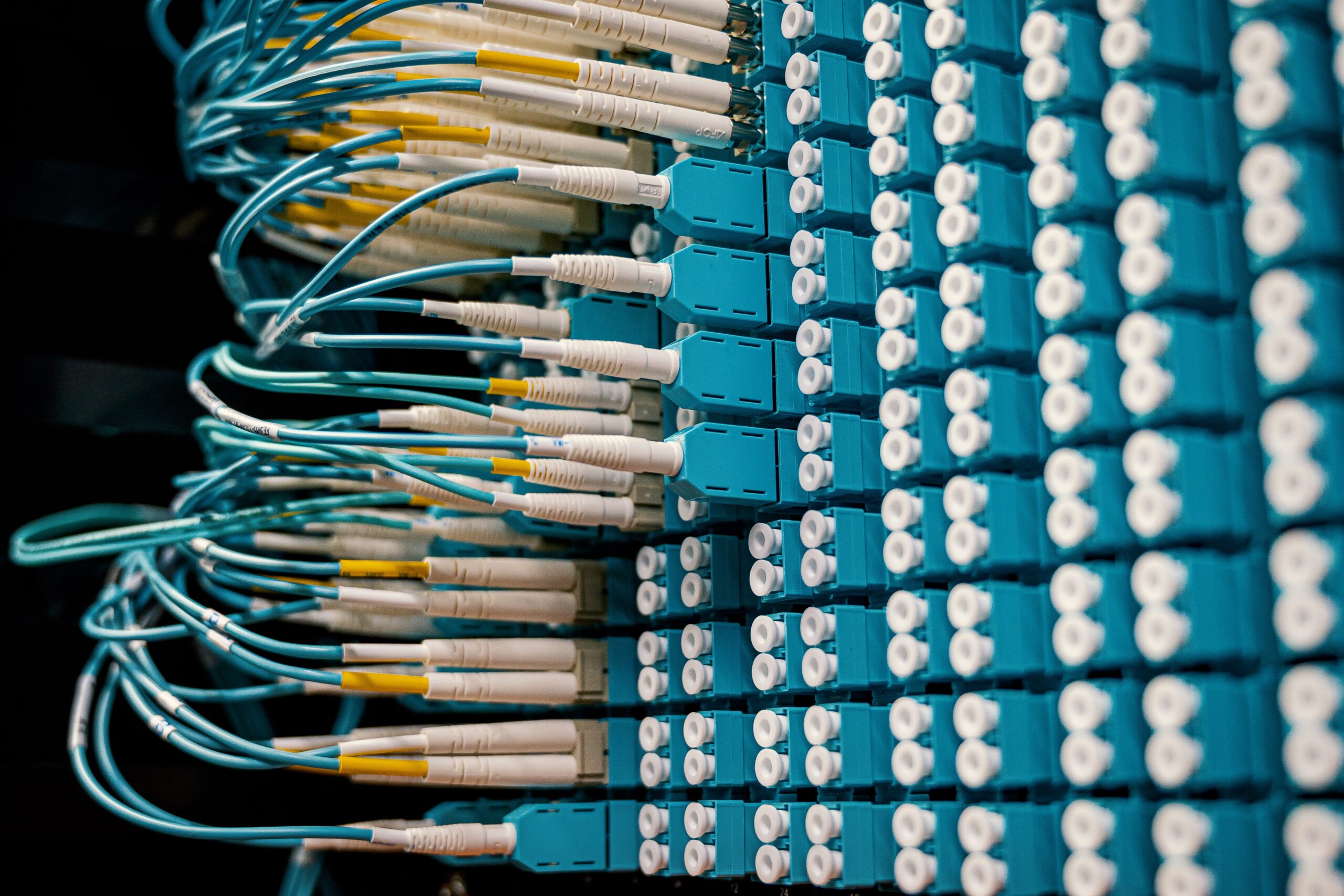
Your SOC center should be built on efficient platform to maximize visibility to threats. It should be flexible to meet your organizations needs and grows as your business grows. Build an adaptive SOC architecture that can continuously evolve your environment and threat scape.
Take advantage of a wide variety of threat intelligence sources and real-time behavioral analytics to detect threats, respond to and neutralize attacks. Use security information management tools that are open and interoperable to enable fast, automated responses. Centralize all critical security information into one single centralized console to reduce human overhead and errors.
Use advanced threat detection and prevention tools:
To enable SOC to support your organization by intelligently and proactively alerting the right people at the right time, you must use advanced threat detection and prevention tools.
IT security personnel must implement various threat management systems to protect IT network from the impact of security events. These systems are intrusion detection systems, antivirus systems, firewalls, operating system logs, and access control systems. They can limit the reach of the compromised system and prevent the spread of the cyber threat.
Though each organization is unique in its current security standards, risk tolerance, and expertise, all share the same goal of preventing cyber attacks. To achieve an effectively operating SOC, the associated processes, people and technologies must be mature, advanced and flexible.
Take time to know your business needs for security operations center based on your security policies and network infrastructure, and then implement the aforesaid steps to build an effective SOC and increase incident response capability.